Mail security is a critical vulnerability, and often unaddressed security gap, for major companies, prominent individuals, governments, and others.
One-third of major corporations report receiving mail-borne threats annually, and many receive more than one.[1]
Revenge from employees, former employees, and other stakeholders is the most common mail threat motive, according to a recent USPIS report.[2] With three simultaneous crises — public health, economic, and social justice — security teams are facing even greater challenges.
Like a pandemic, mail-borne threats often fall into the low probability/high impact category. Six months ago, few businesspeople were concerned with a potential pandemic but its impact has been huge.
In terms of mail security and mail screening, failure to prepare properly has resulted in costly and public evacuations of facilities, injuries, and even deaths.
The risks are not the same for everyone, though.
The Department of Homeland Security and Interagency Security Committee identify some of the risk factors for mail-borne threats as:
| Public Posture | About a dozen industries, including banking, legal, and transportation, are more likely to receive threats |
| Symbolism | Is the organization well-known and controversial? Twitter, Fox News, or The Washington Post, for example, may be more likely targets than a lower-profile organization. |
| Location | Organizations in large, multi-tenant facilities and urban centers are at higher risk. |
| Size | Organizations with large employee counts are more likely to be targets. |
| Volume of mail stream |
There are other intangible factors.
It is also important to note that an organization’s risk can change in response to current events. A recent round of lay-offs, business disruptions, legal proceedings, or even a high-profile or controversial interview from an executive can quickly increase an organization’s risk level.
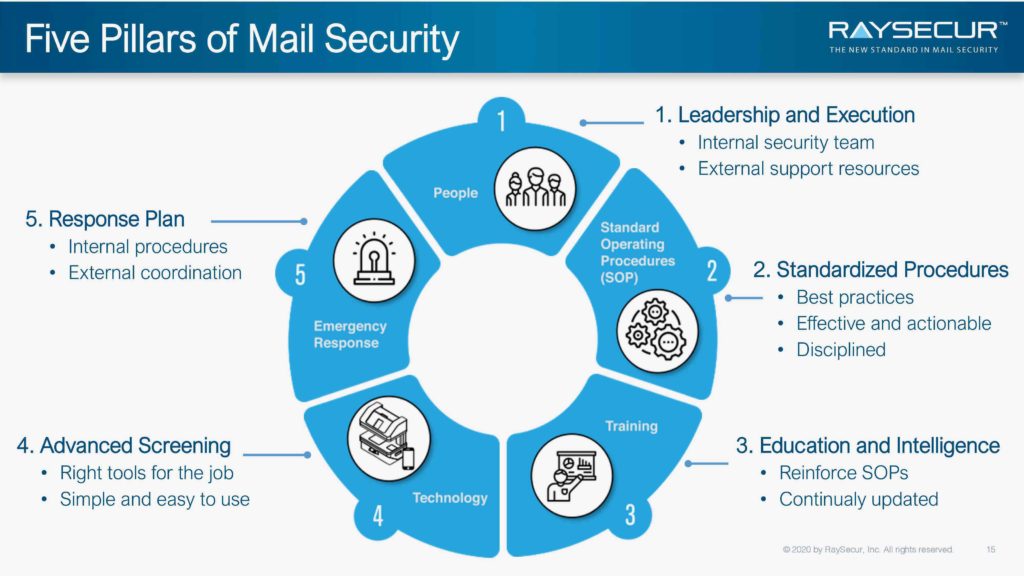
Given the rising number of mail-borne threats, all organizations should have a mailroom security program in place. A comprehensive mail security program rests on these five pillars:
![]()
1. People
Having the right people begins at the top. A company’s executives must be committed to providing the resources for an effective mail security program.
The mailroom team in most organizations will be on-site staff. This provides the organization with the most control and ensures the mail will get to the recipients as quickly as possible. In-house teams are less expensive in the long-run and more likely to detect all threats – they know what their normal mail looks like as well as any risk factors unique to their organization. An added benefit of keeping mail screening in-house is the ability to maintain full control over the privacy of incoming mail.
Some organizations use third-party, off-site screeners. These companies may have expensive technology, like bio-threat detectors and chemical detectors, calibrated to detect specific types of threats. X-ray mail scanners are also useful for screening large boxes, but they cannot detect threats like powders and liquids (which make up the majority of mail threats) that newer, millimeter wave technology can. And if a threat is detected it can be quarantined far from the company’s facility. Companies are, however, limited to the geographic availability of the vendor and mail will be delayed — sometimes by several days — in being delivered.
Most companies do the screening themselves and only use third parties when new or unknown situations arise, or they have a particular gap in their mail security program.
Some companies use a combination of all three approaches depending on the location and threat level of a particular facility. More recently, hybrid approaches have also emerged by providing mail security scanners with remote connection capabilities to mail threat experts. This provides the best of both worlds, by enabling teams to screen mail in-house and call on remote, real-time expert support when and where it is needed.
It is also important to keep in mind that the same approach may not work for all of an organization’s sites. A typical Fortune 500 company with 100+ sites worldwide, requires a flexible and scalable approach to address the different risk levels and logistical requirements of each site. The same systems and technologies used in the corporate headquarters may not be appropriate for a factory, or remote satellite office, and vice versa.
![]()
2. Standard Operating Procedures (SOPs)
To effectively deal with mail-borne threats, companies must systematize their processes with Standard Operating Procedures (SOPs) — and then adhere to them.
Some of the matters that should be included in a mail center SOP include:
- Global company mail handling policy
- Personnel standards, training, and certification
- Standardized mail screening processes
- Suspicious item screening processes
- Mail screening tools and technologies
- Emergency response procedures
A number of factors, such as chain of custody, size of the mail item, and its visual appearance, will help identify the suspicious items that require special screening and attention. These characteristics and handling processes should be considered when formulating SOPs specific to the needs and risk factors of the organization
Large organizations with many facilities will likely prioritize their locations into low-, medium, and high-risk ones and develop a comprehensive set of SOPs to accommodate the particular needs of each. They may also have different procedures for mail with known and unknown chain of custody.
While putting corporate or enterprise-level SOPs in place is a good first step, keep in mind that the SOPs should be reviewed periodically and updated as needed, based on any changes to the organization’s risk level and particular needs.
![]()
3. Training
Ongoing education, training, and coaching is key when it comes to implementing mail screening procedures and ensuring proper use of screening technologies.
Organizations need effective training tailored to the unique roles and responsibilities of people in different positions such as the mail center team, facility and security teams, and general employees that handle or receive mail. Mail security is a team effort and everyone needs to understand how they all come together to protect the organization from mail threats. It is equally important that the team continues to be coached on using the screening technology that the organization has adopted.
In addition to in-person and interactive courses, ongoing education may include ebooks, SOPs, infographics, articles on current mail-borne threats, quarterly webinars, and other materials to deliver current and timely content relevant to the needs of each team member.
It is important that the organizations adopt and encourage continuing education as part of their employee programs. Training programs are offered in-house or outsourced; by numerous organizations such as MSMA and MailCom, to name just a few.
![]()
4. Technology
Mailroom security technology typically falls into two major types: those that can detect threats and those that can identify them.
Detecting threats is sufficient for most organizations: once a potential threat is detected the local hazmat squad or other security organization can be called in to identify what specifically it is and determine its threat level. In the United States, the local Postal Inspector is equipped with a discrete, unmarked vehicle and will come to the facility and provide the first line of defense – keeping the incident out of the media and employees out of harm’s ways.
In the case of threat detection, X-ray scanners can see through large boxes, but they are large; expensive; and require special shielding to contain X-ray radiation, state licensing, and certification. More importantly, the most common mail threats, which include small quantities of hazardous powders (so-called “white powder threats”) and liquids are undetectable with conventional X-ray systems in the quantities sent in most mail threats.
A new type of mail scanner, millimeter wave scanners, can detect more and smaller threats than X-ray scanners and can handle the smaller envelopes and packages in which almost all threats are received. These scanners are ideally-suited to detect not only all of the threats that can be detected with X-ray, but also those that can’t like powders and liquids. Additionally, mmWave imaging is completely safe, uses no harmful radiation, and requires no special certification or licensing.
Law enforcement and related organizations, on the other hand, are most interested in threat identification – sometimes for forensic or prosecutorial needs. Technology to identify the specific nature of the threat includes mass spectrometers, chemical warfare agent detectors, negative pressurized rooms, and other large, expensive laboratory-type equipment. Most organizations don’t need these, though, and would rather leave these tasks to the pros.
![]()
5. Emergency Response
Most organizations use a two-tiered approach when handling emergency response requirements.
They have both Emergency Response Plans (ERP) that mandate how the entire threat is managed and Emergency Action Plans (EAP) that dictate the actions of those involved. These plans need to be prepared and rehearsed. All individuals required for their implementation must be involved to ensure success.
Planning for threats should focus both on the most likely and the most dangerous threats. This provides two courses of action that an organization can adopt when an incident occurs. The core of emergency response planning is to reduce the threat to life, limb, and property.
If at all possible, invite first responders to view and participate in organizational emergency exercise efforts. This increases interoperability and, in the case of an actual emergency response, decreases un-necessary efforts, threats to employees, loss of time and money, and speeds the return to normalcy.
These actions need to be in line with threat reduction. All emergency response efforts and equipment must be readily available and ready to return the organization to a normal state.
Although the risk factors and needs of each organization are unique, by addressing all five pillars of mailroom security a company can put itself in the best position to detect and deal with mail-borne threats when they arrive – as they almost certainly will.
—