
About Will Plummer, CSO
Prior to joining RaySecur as Chief Security Officer, Will spent 25 years in the US Army, where he built an impressive résumé.
- Bronze Star with Valor as a Master Explosive Ordnance Disposal (EOD) Technician
- Commanded multiple Special Operations units with multiple combat deployments
- Trained EOD techs in all 4 US military branches
- Directed VIP support for the last 8 U.S. Presidents
History of Dangerous Mail Threats

1712 Great Britain: Bandbox Plot
The Bandbox Plot of 4 November 1712, was an attempt on the life of Robert Harley, Earl of Oxford, the British Lord Treasurer, which was foiled by the perspicacity of Jonathan Swift (author of “Gulliver’s Travels”), who happened to be visiting the Earl of Oxford.
A bandbox was a lightweight hat-box; this particular one had been configured to fire a number of loaded and cocked pistols on opening, much as a modern-day parcel bomb might be arranged to detonate on opening. In this case, the triggers were attached to a thread; Swift, perceiving the thread, seized the package and cut the thread thus disarming the device. The attack was laid at the door of the Whig party and threw enormous popular sympathy behind Harley.
The event was widely written about in the broadsheets of the time; Swift himself wrote about the occurrence in his A Journal to Stella.
1764 Denmark: First Parcel Bomb
- Hand Carried to Target
- Forced “Victim Operated” Scenario
- Combined “New” Pistol Technology
- Attempted Anti-Tamper Precautions
- “When he opens it, therein is to be found gunpowder and a firelock which sets fire unto it, so he became very injured.”

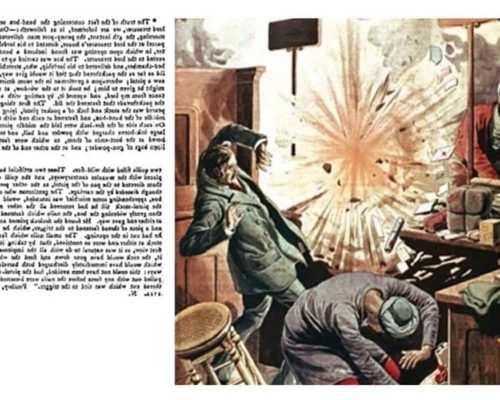
1912-1914 London: Suffragette Bombings
The first terrorist bomb to explode in Ireland in the 20th century was planted not by the IRA, but by the suffragettes.
They also invented the letter bomb; designed to maim or kill those with whom they disagreed.
One of the first bomb attacks carried out by the suffragettes was on the house of chancellor of the exchequer Lloyd George.
According to the Suffragette newspaper, more than 300 incidents of arson and bombing were carried out between 1913 and 1914.
Two homemade bombs from the City of London Police Museum are believed to have been amongst several improvised explosive devices (IEDs) used by the suffragettes during their campaign of violence and extremism.
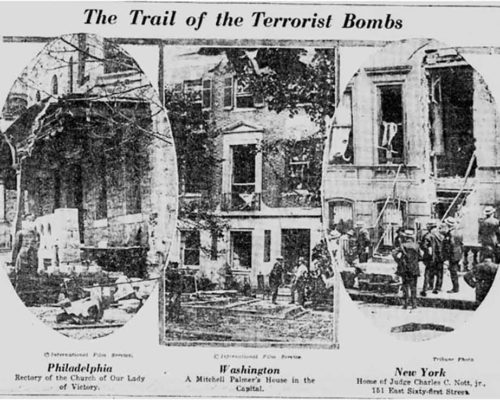
1919 United States: Mass Mail Bomb Attacks
In late April 1919, US Postal Service workers intercepted 36 mail bombs targeting prominent people that had been mailed across the nation.
One of the bombs was delivered to the home of a US senator from Georgia and exploded, injuring the senator’s nurse. Another device was sent to the mayor of Seattle.
When a New York mail clerk read about the attack and the description of the package, he remembered a similar package at the post office where he worked.
Postal authorities were alerted, allowing most of the bombs to be intercepted before they could do any harm.
At least 36 booby trap dynamite-filled bombs were mailed to a cross-section of prominent politicians and appointees, including the Attorney General as well as justice officials, newspaper editors and businessmen, including John D. Rockefeller.

1972-Current: Irish Republican Army (IRA)
In January of 1981, a letter bomb sent to Prime Minister Margaret Thatcher was intercepted by a London postal worker.
In 1983, there were 27 attacks, including letter bombs to Margaret Thatcher and Diana, Princess of Wales.
The majority of the IRA’s bombings did not use mail or postal delivery. Their mail activity was part of a much larger terrorist campaign.
The IRA saw a possible resurgence, after a group calling itself the IRA claimed responsibility for five packages sent to targets across Britain in March of 2019, three of which were discovered in London and one in Glasgow.

1972-1996: Ted Kaczynski, The Unabomber
Ted Kaczynski, known as the Unabomber, is probably the best-known case of mail bombs in the United States.
Between 1978 and 1994, the Unabomber sent multiple bombs through the mail, killing or injuring more than a dozen victims.
In 1979, one of his bombs was placed in the cargo hold of a commercial airplane. Only a faulty timing mechanism prevented the bomb from exploding.
Kaczynski, once a successful academic, wrote letters in attempts to justify his killing.
Ultimately it was one of his letters which led to his arrest. His own family recognized the language and writing style of his so-called “manifestos,” and alert authorities.

1980: Harvey's Casino Bombing - Lake Tahoe, NV
The Harvey’s device has been described by the FBI as “undefeatable.”
It had as many as 8 fusing systems, which would cause it to detonate if it were tampered with, and it was delivered to the building hours before detonation.
The box contained 700 lbs of TNT- equivalent explosive material and 6 lbs of military C-4.
John Birges needed money. His restaurant business was failing.
His massive bomb was an extortion to get money to save his business. He chose Harvey’s casino because he had lost money there.
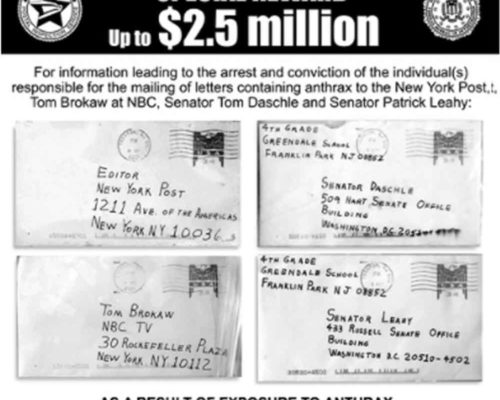
2001-Current: Anthrax
A wave of fear swept across Washington, prompting many people to take antibiotics in case they had somehow been exposed.
When it was all over, the packages had killed five people and sickened 17 others.
Letters that were sent to then-Senate Majority Leader Tom Daschle and Sen. Patrick Leahy declared “Death to America. Death to Israel.”
Although the FBI interviewed more than 9,100 people and issued more than 6,000 subpoenas in the case, no one has been convicted.
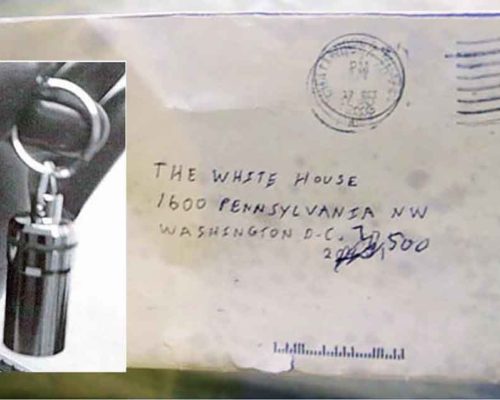
2003-Present: Ricin
Unfortunately, dangerous mail attacks via toxic substances like ricin are likely to be on the rise.
In 2020, a Canadian woman mailed ricin to the U.S. White House and was arrested and charged for her crime.
In early 2021, Dr. Anthony Fauci said that he received a white powder letter and feared for his life, worrying he might be covered in ricin powder.
- Low-tech “legal” threat
- Most often powdered and in small amounts (50mg)
- Injected, ingested, or absorbed
- Primarily used against high-profile targets
- Often aimed at political targets
Types of Dangerous Mail Threats

White Powder
- Two general forms
- 2,500-5,000 milligrams
- 50-200 milligrams
- Often tied to an external event
- Most often insider or known threat
- High profile target for sender

Hoaxes
- Aimed as personal “opposition” to political values
- Widespread
- High-profile targets
- Mentally unstable
- No viable devices
- Mandated emergency response

Modern Mail Bombs
- Rare but extremely dangerous
- Multiple packages sent in rapid succession
- Generally time- or victim-operated
- Usually tied to grievance
- Quick apprehension
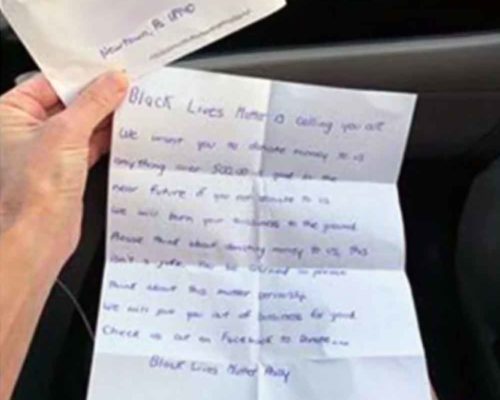
Extortion / Threatening Messages
- Generally regional
- Politically or emotionally driven
- Poorly written and easy to identify in screening
- Generally empty threats
- Quickly turns into federal investigation
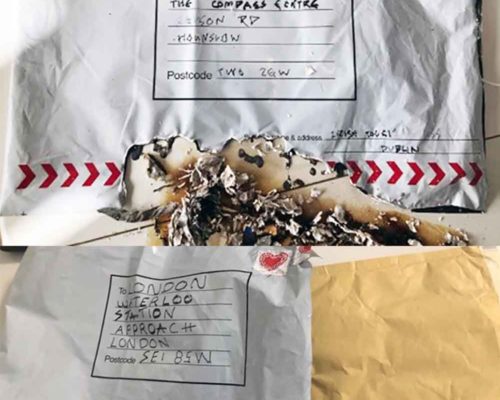
Incendiary
- “Revised” incendiary devices
- Soft packages intended to send a message
- Historical IRA devices used timers set for several days
- 10 years between similar events
- High failure rate
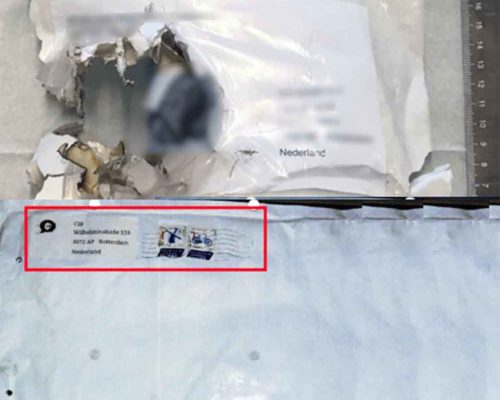
2020 Dutch Incidents
These incidents from 2020 came in several waves and used incendiary devices (and white powder) to disrupt businesses across the Netherlands.
We covered these events as they happened, in February and November.
- Devices mailed to many Dutch business
- Burned instead of detonating
- False return addresses
- Real company
- No responsibility
- Mixture of bombs and threatening letters
- Bitcoin extorsion

Non-Standard Threats
Any “creative” example. In one memorable case: land mines.
- Suspected improvised explosive device was found by the mail carrier…The fuse was ignited but failed to burn causing a malfunction
- The witness stated that the item had been mailed to him with no return address on the package. Item was identified as a TM-62 landmine with fuze installed
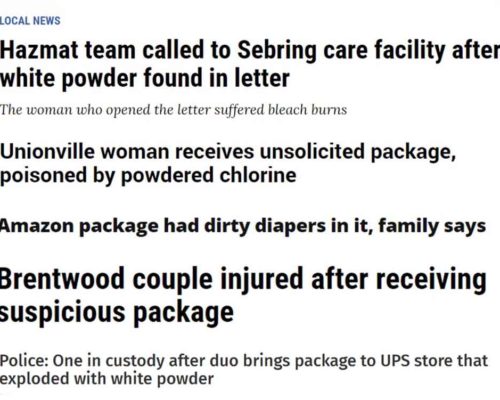
Hazmat
- Generally over-the-counter Items
- Not a 911 event
- Mail is inherently dirty
- PPE, PPE, PPE
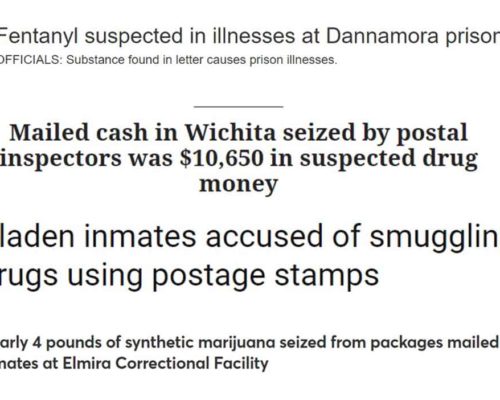
Drugs
- Increasingly common
- Every form imaginable
- Every location imaginable
- Liquid
- Pills
- Brick powder
- Loose powder increasing
- Fentanyl, Meth, Cocaine
What’s next?
Implementing a mail security program is often the missing link in a comprehensive physical security program.
It is unfamiliar to many and may present challenges to those who are new to the world of mail security.
RaySecur can help implement a sound mail center security practice and bridge the gap in your facility’s physical security.

